Continuously map shadow APIs, detect logic flaws, and block runtime abuse across your entire API ecosystem. Eliminate unknown API exposure and automate pen-testing 24x7 without manual effort.
Join Waiting listAutomatically scans network traffic, API gateways, and code repositories to surface shadow, rogue, and zombie APIs into a continuously updated live inventory with risk posture
Identifies PII, credentials, tokens, and financial data inside API payloads and responses to prevent data leakage and maintain regulatory compliance requirements
Runs continuous API pen-tests covering OWASP API Top 10, business logic flaws, authentication bypasses, and injection vulnerabilities 24x7 without manual scheduling
Maps legitimate API user journeys and detects behavioral deviations indicating scraping, credential stuffing, or multi-step fraud attack patterns
Monitors live API traffic and instantly blocks policy violations, abuse patterns, and anomalous request sequences before they cause organizational damage
Provides unified visibility into API inventory health, test coverage, vulnerability status, and sensitive data exposure risk across all environments
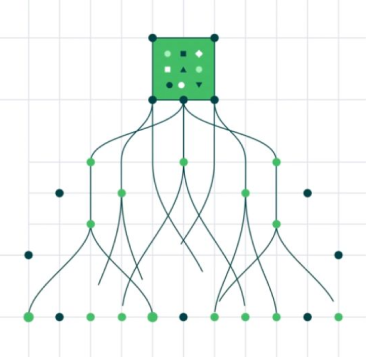
Discovers and eliminates unknown API exposure including shadow and rogue endpoints across the environment
Test Productivity - Replaces manual quarterly testing cycles with continuous automated security coverage operating 24x7 without human scheduling - 5X
Reduces sensitive data exposure by proactively detecting API payload leakage paths before exploitation by attackers
Ensures complete API inventory visibility eliminating blind spots in the organization's application security posture
Turn operational complexity into measurable performance gains.